What Can I Do to Protect My Business from Unexpected Disasters?
Developing a Robust Disaster Recovery Plan for Business Continuity
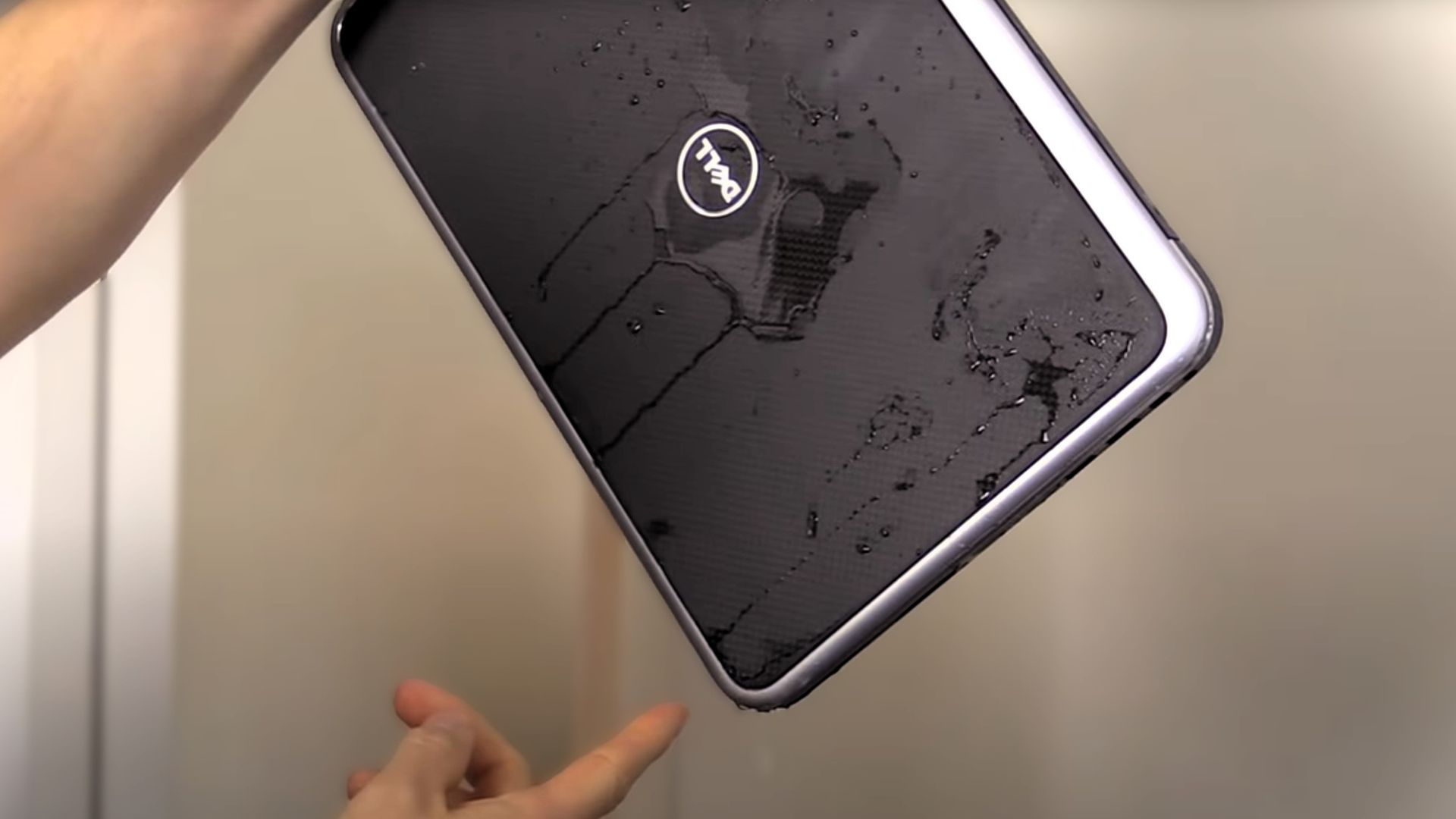
If you think disasters only happen to others, think again. Small businesses are particularly vulnerable to data loss and operational halts, often lacking robust disaster recovery plans. It's a glaring oversight that can spell the end of your business. So, what can you do to ensure that your business is prepared for the unexpected?
The Solution: Create a Comprehensive Disaster Recovery Plan (DRP)
The key to protecting your business from disasters is to create a comprehensive Disaster Recovery Plan (DRP) that covers all the essential aspects of business continuity. This plan should include strategies for data backup, hardware replacement, and emergency communication, ensuring that your business can weather any storm.
Actionable Tip: Identify Critical Systems and Establish Offsite Backups
To create an effective DRP, start by identifying your business's critical systems and data. These are the assets that are essential to your operations and cannot be easily replaced. Once you've identified these critical elements, establish offsite backup locations to ensure that your data is always safe and accessible, even in the event of a disaster. Finally, test your DRP quarterly to ensure its efficacy and make any necessary updates.
The Non-Negotiable Benefits of a Disaster Recovery Plan
- Ensured Business Continuity: A well-laid DRP ensures that your business operations are minimally affected by unforeseen events. By having a clear plan in place, you can quickly recover from disasters and get back to business as usual.
- Increased Customer Confidence: Transparency about your DRP can significantly boost customer trust, reinforcing your business's reliability. When customers know that you have a plan in place to handle emergencies, they feel more confident in your ability to deliver products or services consistently.
- Maintained Regulatory Compliance: Certain industries, such as healthcare and finance, mandate a disaster recovery plan for compliance. By having a DRP in place, you not only keep your business legal but also save yourself from potential fines and legal repercussions.
Don't Wait Until It's Too Late
Forewarned is forearmed. An efficient Disaster Recovery Plan is a non-negotiable asset for any forward-thinking business. Don't wait until disaster strikes to start thinking about your recovery strategy—by then, it may be too late.
Get Expert Help to Create Your Custom DRP
To ensure that your DRP is comprehensive and tailored to your unique business needs, consider partnering with HCS Technical Services. Their experienced team can help you identify your critical systems, establish secure backup processes, and create a plan that keeps your business running smoothly, no matter what challenges come your way.
Protecting your business from unexpected disasters is not just a smart move—it's a necessary one. By creating a comprehensive Disaster Recovery Plan and testing it regularly, you can rest assured that your business is ready for anything. Don't get caught off guard—start building your ultimate shield against disasters today.
HCS Technical Services











