The Dark Side of Browser Extensions: Understanding the Risks and Safeguarding Your Online Presence
Safeguarding Your Online Presence: The Importance of Browser Extension Security
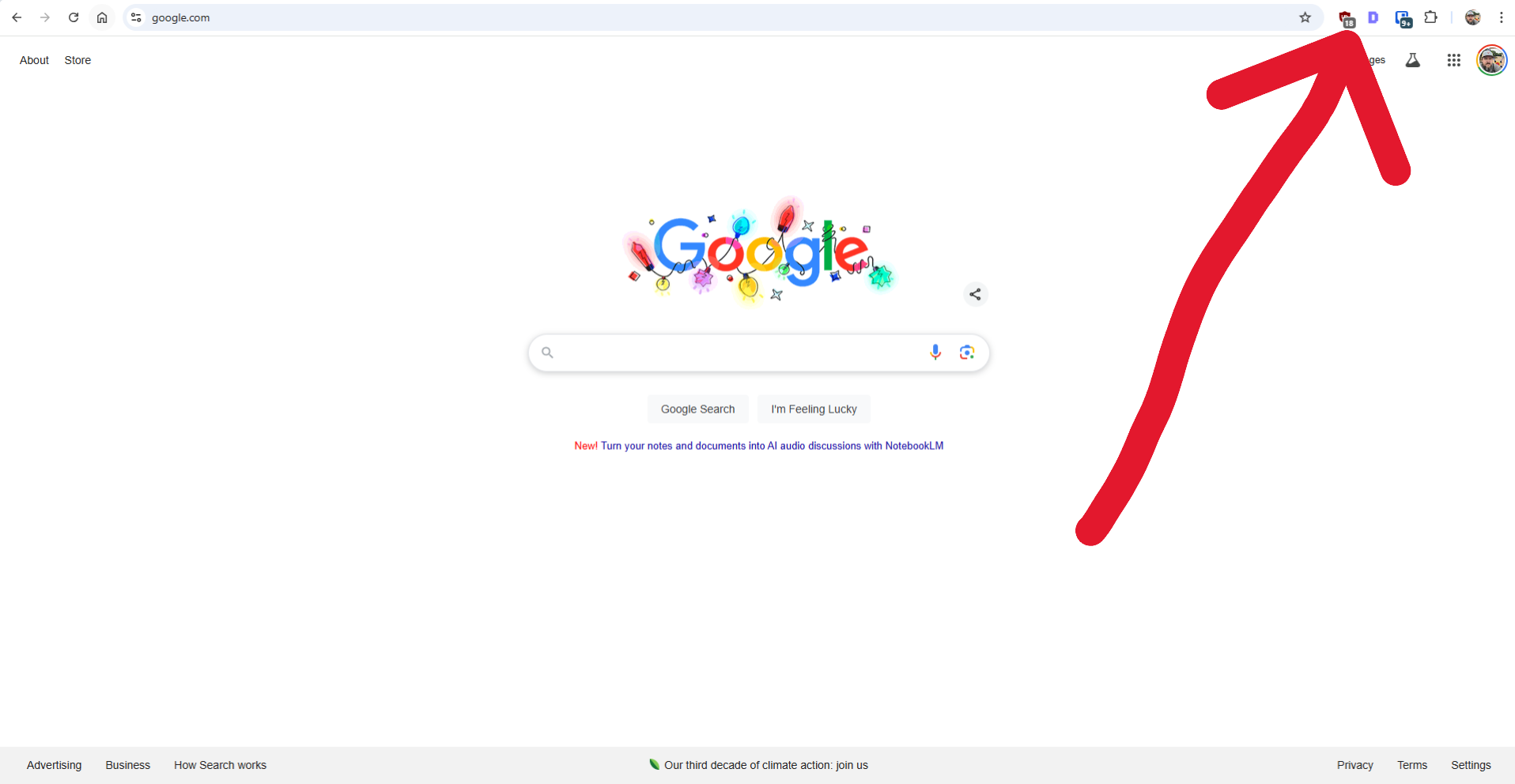
Browser extensions have become an integral part of our online experience, offering a wide range of functionalities and customization options. With over 176,000 extensions available on Google Chrome alone, it's easy to get caught up in the excitement of adding new features to our browsers. However, beneath the surface of these seemingly harmless extensions lies a complex web of potential security risks and threats to our online privacy.
The Allure and Perils of Browser Extensions
Browser extensions are modules that users can add to their web browsers, extending functionality and adding customizable elements. From ad blockers and password managers to productivity tools, the variety is vast. However, the ease with which users can install these extensions also introduces inherent security risks.
Key Risks Posed by Browser Extensions
- Privacy Intrusions: Many browser extensions request broad permissions, which can compromise user privacy if abused. Certain extensions may overstep their intended functionality, leading to the unauthorized collection of sensitive information.
- Malicious Intent: Some extensions harbor malicious code, which can exploit users for financial gain or other malicious purposes. These rogue extensions may inject unwanted ads, track user activities, or even deliver malware.
- Outdated or Abandoned Extensions: Extensions that are no longer maintained or updated pose a significant security risk. Outdated extensions may have unresolved vulnerabilities, which hackers can exploit to gain access to a user's browser and potentially compromise their entire system.
- Phishing and Social Engineering: Some malicious extensions engage in phishing attacks and social engineering tactics, tricking users into divulging sensitive information.
- Browser Performance Impact: Certain extensions can significantly impact browser performance, leading to system slowdowns, crashes, or freezing.
Mitigating the Risks: Best Practices for Browser Extension Security
- Stick to Official Marketplaces: Download extensions only from official browser marketplaces, which have stringent security measures in place.
- Review Permissions Carefully: Before installing any extension, carefully review the permissions it requests. Limit permissions to only what is essential for the extension's intended purpose.
- Keep Extensions Updated: Regularly update your browser extensions to ensure you have the latest security patches.
- Limit the Number of Extensions: Only install extensions that are genuinely needed, and regularly review and uninstall those that are no longer in use.
- Use Security Software: Use reputable antivirus and anti-malware software to add an extra layer of protection against malicious extensions.
- Educate Yourself: Stay informed about the potential risks associated with browser extensions, and understand the permissions you grant.
- Report Suspicious Extensions: If you encounter a suspicious extension, report it to the official browser extension marketplace and your IT team.
- Regularly Audit Your Extensions: Conduct regular audits of the extensions installed on your browser, and remove any that are unnecessary or pose potential security risks.
Contact Us for Help with Online Cybersecurity
Browser extensions are just one way you or your employees can put a network at risk. Online security is multi-layered, and includes protections from phishing, endpoint threats, and more. Don't stay in the dark about your defenses – we can assess your cybersecurity measures and provide proactive steps for better protection.











