AI Driven Predictive Maintenance for Cost and Downtime Reduction
AI Driven Predictive Maintenance for Cost and Downtime Reduction
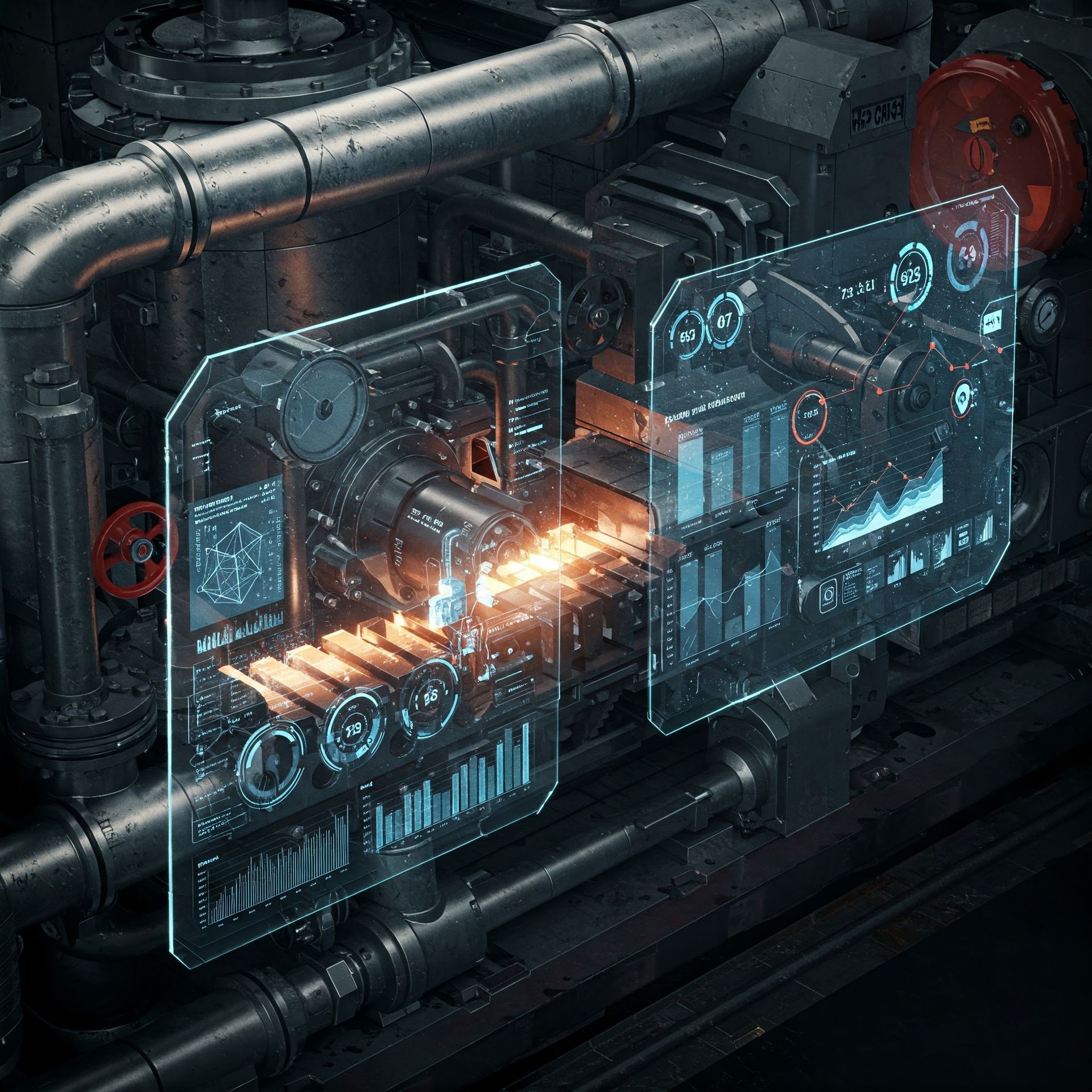
Understanding AI Driven Predictive Maintenance
Artificial Intelligence (AI) has revolutionized many facets of modern industry, and predictive maintenance is one area where its impact is profoundly felt. Predictive maintenance refers to the use of advanced analytics techniques to anticipate maintenance needs before failures occur. This approach significantly reduces unexpected equipment downtimes and reduces maintenance costs by allowing interventions only when necessary. The integration of AI in predictive maintenance entails the use of machine learning algorithms and data-driven insights to monitor equipment performance in real-time. By continuously analyzing data from multiple sources, such as sensors and historical maintenance records, AI models can predict when a piece of machinery is likely to fail. This foresight allows organizations to carry out maintenance activities at optimal times, thereby minimizing disruptions to operations and extending the lifespan of critical equipment. The benefits of AI-driven predictive maintenance extend beyond cost efficiency, as they also lead to better resource allocation and improved overall productivity.
The Cost-Saving Advantages of Predictive Maintenance
The primary appeal of predictive maintenance lies in its potential to generate substantial cost savings for businesses. Traditional maintenance strategies often operate on a reactive or scheduled basis, which can either lead to unnecessary parts replacements or failure to prevent breakdowns entirely. In contrast, predictive maintenance allows companies to address maintenance issues only when needed, optimizing the use of their maintenance budgets. By identifying potential failures before they occur, organizations can avoid the costly emergency repairs and the significant loss of productivity associated with unexpected equipment downtime. Furthermore, predictive maintenance helps in better inventory management, as it enables businesses to prepare for specific maintenance needs in advance, ensuring that they have the right parts available at the right time. Investing in AI-driven predictive maintenance tools allows for more informed decision-making regarding maintenance scheduling, ultimately leading to a reduction in overall operational costs and an increase in profit margins.
Reducing Downtime with AI Technologies
- AI-driven predictive maintenance effectively minimizes equipment downtime by predicting failures before they happen, allowing for planned maintenance activities.
- This proactive approach enables companies to maintain smooth operations and uphold service level agreements, avoiding potential penalties associated with unplanned outages.
- Utilizing AI technologies, such as predictive analytics and machine learning, helps identify failure patterns and anomalies that could indicate impending equipment malfunctions.
- By addressing these issues promptly, businesses can prevent disruptions and maintain continuous production, boosting customer satisfaction and reputation.
The Future of Maintenance: Integrating AI for Success
As AI technology continues to evolve, its integration into maintenance strategies offers promising prospects for businesses striving for operational excellence. The future of maintenance will likely see even more sophisticated AI systems, capable of intricate predictive analysis and decision-making. The incorporation of IoT devices further enhances AI-driven maintenance by providing a continuous stream of data, enabling real-time adjustments and more accurate predictions. Companies that embrace these advancements will not only benefit from enhanced maintenance efficiency but will also gain a competitive edge by delivering more reliable products and services. Training the workforce to understand and leverage AI tools is crucial, ensuring that organizations can fully capitalize on this technology's potential. Additionally, collaboration between AI experts and industry practitioners will drive innovation, yielding smarter maintenance solutions. With AI's ability to offer actionable insights and foresight, the future of maintenance is poised for significant transformation, bringing cost savings, reduced downtime, and improved operational resilience. Embracing AI-driven predictive maintenance is essential for businesses aiming for sustainable growth and long-term success in a rapidly evolving digital world.











